In the world of digital finance, the traditional concept of “ownership” has been completely rewritten. We are no longer just managing accounts; we are managing cryptographic control. At the center of this shift is a strategic choice between two distinct paths: Non-Custodial Wallets 及 Managed Institutional Custody.
One offers the original blockchain promise of absolute self-sovereignty, while the other provides the professional governance and risk mitigation required for institutional-scale operations. For any organization, the right choice depends on how you balance the need for unilateral control against the necessity of fiduciary-grade security.
Defining the Models of Control
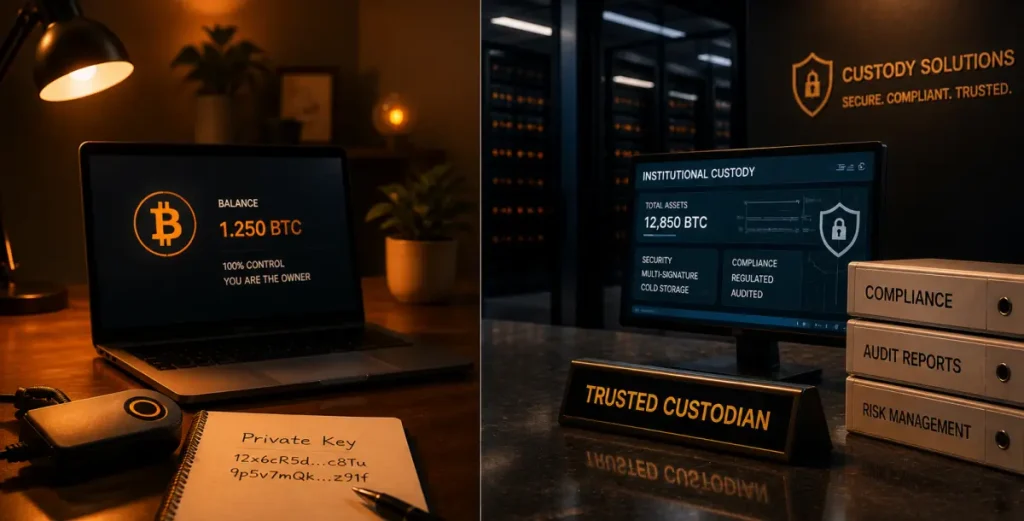
Sovereign (Non-Custodial) Custody
This is the “self-managed” framework. In a non-custodial architecture, private keys are generated and stored locally at the “edge” (on your own device). As the service provider has zero visibility into your key material, they have no power to move, freeze, or—crucially—recover your funds. This is the ultimate tool for censorship resistance, but it removes any safety net. In this model, you are your own bank, which means you are also your own security firm.
Managed Institutional Custody
Managed custody is a third-party fiduciary model. Here, a regulated provider secures the keys within hardened infrastructure, such as Hardware Security Modules (HSMs) or through Multi-Party Computation (MPC). This approach introduces governance guardrails, such as multi-tier approval workflows and automated audit trails, that align with traditional corporate standards.
Strategic Trade-offs: Autonomy vs. Governance
Agility at the Edge: The Case for Self-Custody
Non-custodial systems are built for unfiltered execution. Because there is no intermediary to approve a transaction, you can move assets instantly to react to market volatility or interact directly with DeFi protocols. This “zero-latency” environment is perfect for active trading, but it introduces significant execution risk. Without institutional guardrails, the organization is vulnerable to local threats like private key exfiltration or simple human error.
Operational Integrity: The Case for Managed Custody
Institutional custody is engineered to eliminate single points of failure. By using MPC or HSMs, providers ensure that a private key never exists in an unencrypted or singular state. The real value here is the audit trail. For a corporate board, having a documented policy engine—where transactions require “M-of-N” authorizations from different stakeholders—is a baseline requirement for internal controls and regulatory compliance.
Comparison at a Glance: The Risk Matrix
| Feature | Sovereign (Non-Custodial) | Managed Institutional Custody |
| Key Lifecycle | Generated locally at the “Edge” | Distributed (HSM / MPC) |
| Signing Logic | Unilateral (Single Signature) | Multi-Tiered Authorization |
| Disaster Recovery | Physical Seed Phrase Backup | Identity-based Recovery Protocols |
| Attack Surface | Local Device & User Error | Infrastructure & Vendor Risk |
| Compliance | Self-attestation | SOC 1 / SOC 2 / Regulated |
The Institutional Security Stack: Defense-in-Depth
Modern enterprise systems rarely rely on a single layer of protection. Instead, they utilize a multi-layered strategy to harden the environment:
- Tiered Storage: Moving the vast majority of capital into air-gapped, Cold Vaults for long-term preservation, while keeping only operational funds in “warm” environments.
- MPC Orchestration: Sharding key material across multiple nodes so that a single compromised device cannot lead to a total loss of funds.
- Velocity Throttling: Automated governance engines that flag or block anomalous outflows based on pre-set spending limits or time-based “cool-off” periods.
- Real-Time Screening: Integrated AML tools that scan destination addresses against sanction lists before a transaction is ever broadcast to the blockchain.
The Hybrid Convergence: A Layered Strategy
As the digital asset market matures, the binary choice between “Self-managed” and “Managed” is fading. Most sophisticated entities are moving toward a Hybrid Custody model that diversifies risk:
- Working Capital: Utilizing non-custodial wallets for agile market positioning and direct interaction with the on-chain ecosystem.
- Core Treasury Reserves: Utilizing Qualified Custodians to satisfy institutional mandates, fulfill insurance requirements, and ensure board-level oversight.
Ownership as a Governance Strategy
Non-custodial and managed custody are tools designed for different threat models. One prioritizes the autonomy of the user; the other prioritizes the resilience of the organization.
For the modern professional, the goal is to integrate these tools into a comprehensive Asset Governance Framework. In today’s digital economy, your level of control is measured by how effectively you eliminate single points of failure while maintaining the agility to move with the market.