In digital asset management, private key security has traditionally been a zero-sum game between protection and accessibility. Institutional storage methods typically force a choice between two extremes: cold storage, which is secure but operationally rigid, and hot wallets, which offer convenience but remain vulnerable to network-based attacks.
Multi-Party Computation (MPC) resolves this paradox. By utilizing advanced cryptographic frameworks, MPC enhances asset liquidity without compromising security, fundamentally restructuring the architecture of digital asset custody.
Core Principles of MPC
MPC is a cryptographic framework that enables multiple parties to jointly compute a function while keeping their individual inputs private. In the context of institutional custody, MPC is applied to Distributed Key Generation (DKG) and Collaborative Signing.
To understand the value of MPC, it is necessary to compare it to traditional key management:
- Single-Secret Model: Standard private keys exist as a single, complete string of data. This creates a central point of failure: if the key is compromised, control is lost; if it is misplaced, access is permanently denied.
- MPC Distributed Model: Under an MPC framework, a “complete” private key never exists in any single location—not during generation, storage, or the signing process.
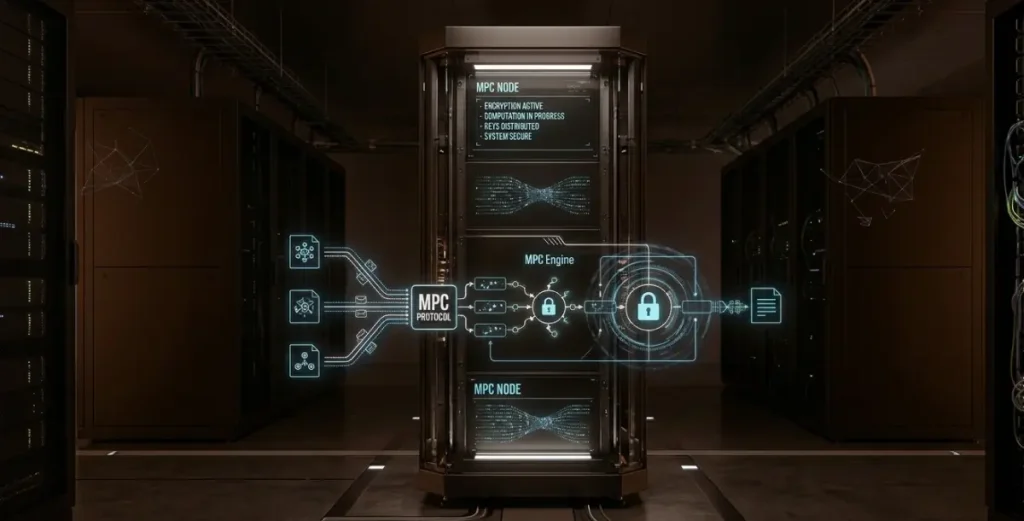
Technical Workflow
The MPC lifecycle ensures that sensitive data is never centralized, utilizing three primary stages:
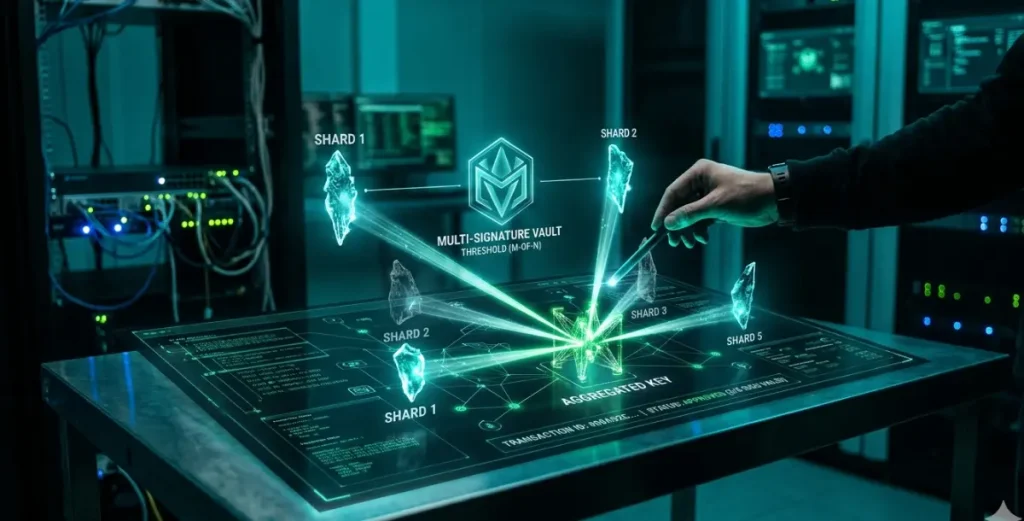
- Distributed Key Generation (DKG): Instead of a single device generating a key, multiple independent nodes collaborate to create mathematical “shards.” Each node retains its own shard, which provides no actionable information in isolation.
- Threshold Signing: When a transaction is initiated, the required number of nodes perform a collaborative computation to produce a valid digital signature. Critically, these shards are never exchanged or combined to form a full key during the process.
- Persistence and Security: After the signature is broadcast to the blockchain, the shards remain within their respective secure environments. The full private key is never reconstructed in memory or on disk, maintaining an ongoing defense against unauthorized access.
MPC vs. Traditional Multi-Sig
While MPC and Multi-Signature (Multi-Sig) both distribute control, they operate at different layers of the blockchain stack.
| Feature | Traditional Multi-Sig | Multi-Party Computation (MPC) |
| Verification Layer | On-chain (Smart Contract) | Off-chain (Cryptography) |
| Transaction Appearance | Visible as a multi-party txn | Appears as a standard single-signature txn |
| Network Compatibility | Must be supported by the protocol | Chain-agnostic (Works on any chain) |
| Transaction Fees | Higher (Multiple signatures = more gas) | Lower (Single signature gas cost) |
| Privacy | Low (Signer identities/count revealed) | High (Signer details remain hidden) |
Key Distinction: The primary distinction between Multi-Signature (Multi-Sig) and Multi-Party Computation (MPC) lies in where the signature validation occurs and how it impacts network compatibility:
- Multi-Signature (On-Chain): Requires the underlying blockchain protocol to natively support, recognize, and validate multiple independent signatures. This increases transaction size, elevates gas costs, and can be limited by a network’s specific smart contract or scripting capabilities.
- MPC (Off-Chain): Generates a single, standard signature through distributed computation before reaching the blockchain. This ensures universal compatibility with any network—including Bitcoin—while significantly reducing transaction fees and enhancing institutional privacy by obscuring the underlying signing structure.
Institutional Applications of MPC in Digital Asset Custody
Multi-Party Computation (MPC) is shifting digital asset custody from centralized “vault” models toward distributed control frameworks. This transition addresses critical security, liquidity, and governance requirements for professional entities.
1. Risk Mitigation and Security
- Elimination of Single Points of Failure: Unlike traditional custody where a full private key resides in a single server or HSM, MPC eliminates the central target. Attackers must breach multiple geographically and logically isolated nodes simultaneously to reach the signing threshold (M-of-N).
- Internal Fraud Prevention: Since no single individual holds a full key, collusion becomes significantly more difficult when key shards are distributed across disparate departments or jurisdictions.
- Disaster Recovery: Key shards can be backed up independently. Because an individual shard holds no inherent value, backup security is simplified while maintaining high redundancy; the loss of a single node does not result in the permanent loss of assets.
2. Operational Efficiency and Liquidity
- “Warm” Storage Capabilities: Traditional cold storage often requires manual, physical intervention, leading to significant latency. MPC enables “Warm Storage”—combining the security of cold storage with near-instant execution. Shards stored in secure cloud environments or HSMs can respond in milliseconds once authorized.
3. Governance and Advanced Policy Engines
MPC enables highly granular authorization policies tailored to institutional workflows:
- Tiered Thresholds: e.g., 2-of-3 signatures for transactions more than $100k OR 5-of-7 for larger transfers.
- Role-Based Access Control (RBAC): Requiring specific departmental signatures (e.g., Legal and Treasury) to validate a transaction.
- Temporal Restrictions: Implementing time-locks to restrict signing windows.
Core Institutional Advantages
- Privacy: Off-chain signing keeps internal governance and organizational structures private from the public ledger.
- Auditability: Internal logs provide a comprehensive audit trail for compliance and regulatory reporting without exposing sensitive cryptographic data.
- Defense in Depth: The integration of MPC with Trusted Execution Environments (TEEs) and Hardware Security Modules (HSMs) combines mathematical cryptographic rigor with physical hardware isolation.
Implementation Considerations
- Protocol Integrity: Deployment should focus on peer-reviewed protocols (e.g., GG18 or MPC-CMP) that have undergone rigorous security audits.
- Network Latency: Multi-round communication between nodes is required for signing. Network performance is a critical factor, particularly in high-frequency trading (HFT) environments.
- Identity & Access Management (IAM): Security often shifts from the key to the authorization layer. Robust Multi-Factor Authentication (MFA) and biometric verification are essential to secure the individuals triggering shard participation.
The Future of Institutional Custody
As the digital asset market matures, MPC is transitioning from an emerging technology to a standard infrastructure requirement. For institutions managing significant capital, MPC provides the necessary framework for a secure, transparent, and liquid asset management ecosystem.