In an era where data privacy and decentralized infrastructure are central to global discourse, the primary challenge is enabling collaborative computation without exposing raw data. Multi-Party Computation (MPC) has emerged as a key cryptographic solution, allowing organizations to utilize data while maintaining absolute privacy.
For financial institutions, digital asset custodians, and enterprise data governors, MPC represents a shift from “securing the perimeter” to “securing the computation itself.”
What is Multi-Party Computation (MPC)?
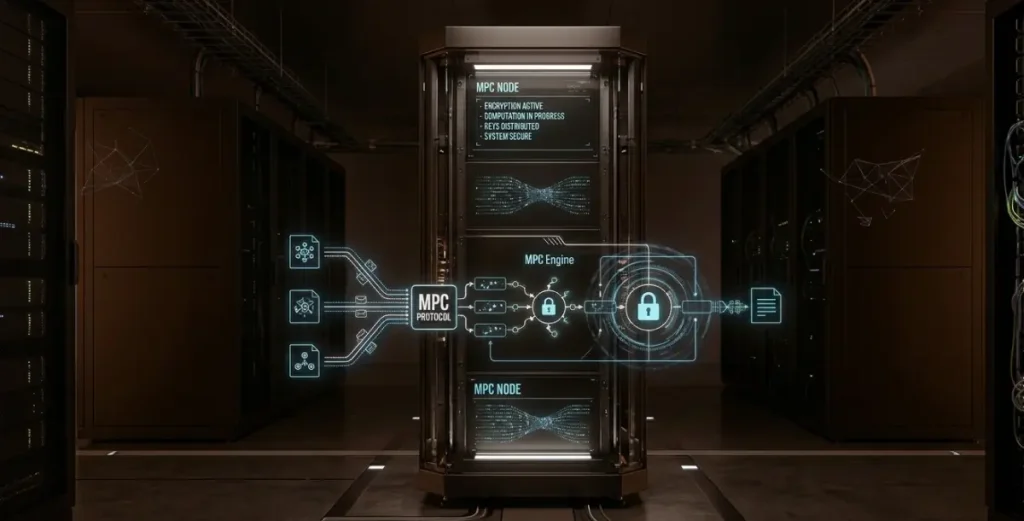
Multi-Party Computation is a subfield of cryptography that allows multiple parties to jointly compute a result based on their individual data inputs, while keeping those inputs private from one another.
The core philosophy of MPC is that data remains usable but invisible, and collaboration is achieved without compromising individual privacy. Unlike traditional systems that require data to be decrypted and centralized for processing, MPC ensures that:
- Collaborative Risk Assessment: Institutions can calculate a joint risk score without sharing their underlying customer databases.
- Key Management: Multiple key holders can generate a digital signature without ever reconstructing the full private key in a single location.
Core Principles: Secret Sharing and Distributed Logic
MPC utilizes cryptographic primitives to distribute trust and eliminate central vulnerabilities.
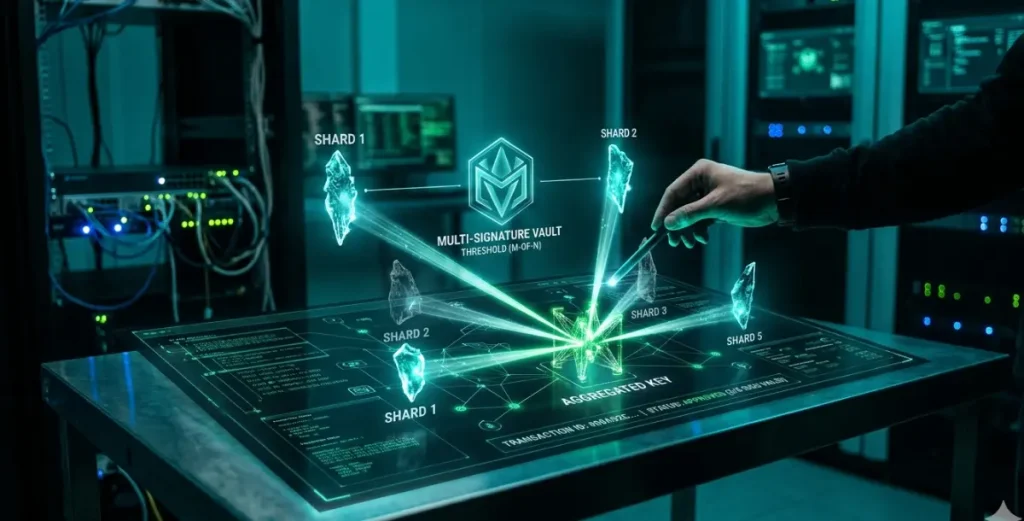
Secret Sharing
A sensitive input—such as a private key or a financial record—is mathematically split into multiple “shards” or “shares.”
- Each participant holds only one shard.
- A single shard provides zero information about the original data.
- The complete data set is never reconstructed in its entirety during the computation process.
Distributed Collaborative Computation
Participants perform mathematical operations on their respective shards locally. They exchange encrypted intermediate results—rather than raw data—to reach a collective output.
- Encrypted Processing: The computation occurs in a “blinded” state, where the participants cannot see the values they are calculating.
- Result-Only Disclosure: Participants only see the final, authorized output, ensuring that the inputs provided by other parties remain confidential.
Strategic Advantages of MPC Technology
- Elimination of Centralized Risk: By moving away from centralized databases, MPC removes the “honey pot” effect that attracts hackers. Even if one or more nodes are compromised, the total data remains inaccessible.
- High-Integrity Privacy: It enables compliance with strict global data protection regulations (like GDPR) by allowing data analysis without data movement.
- Zero-Trust Architecture: MPC reduces reliance on “trusted third parties.” Participants can collaborate with competitors or external vendors without granting them access to proprietary information.
- Resilient Key Management: In the crypto industry, MPC is the leading solution for securing high-value wallets, as it prevents the total loss associated with a single stolen or lost private key.
MPC in Digital Asset Management
The most transformative application of MPC is in Institutional Digital Asset Custody. This shift is “transformative” because it fundamentally changes the security model: instead of relying on a physical vault or a single piece of hardware to protect a secret, security is derived from a decentralized mathematical process. This allows institutions to manage billions in assets without ever having a single “master key” that could be stolen or lost.
- Distributed Key Generation (DKG): Private keys are generated as distributed shards across multiple servers or devices from the outset. A “complete” key never exists at any point in the lifecycle.
- Threshold Signatures: To authorize a blockchain transaction, a predefined number of shards (the threshold) interact to produce a standard signature. To the blockchain, it looks like a normal transaction, but the security behind it is decentralized.
- Institutional Risk Control: Custodians use MPC to require approvals from different departments—such as compliance, treasury, and security—ensuring that no single employee can unilaterally move assets.
Comparative Analysis: MPC vs. Traditional Security
| Feature | Traditional Encryption | Multi-Party Computation (MPC) |
| Data State | Encrypted at rest, decrypted for use | Encrypted throughout the process |
| Processing | Centralized | Distributed |
| Single Point of Failure | Exists (Decryption server) | Eliminated |
| Data Sovereignty | Data is shared with the processor | Data never leaves the owner’s server |
| Trust Model | Trust in the service provider | Trust in cryptographic math |
Technical Implementation Pillars
- Secret Sharing Algorithms: Sophisticated math (like Shamir’s Secret Sharing) that determines how data is split and reconstituted.
- Homomorphic Encryption: A mechanism allowing mathematical operations to be performed on encrypted text, yielding an encrypted result that, when decrypted, matches the result of operations performed on the plaintext.
- Garbled Circuits: A protocol that allows two parties to evaluate a function without either party learning anything about the other’s input.
- Zero-Knowledge Proofs (ZKP): Often used alongside MPC to prove that a specific shard or computation is valid without revealing the underlying information.
Operational Challenges
Despite its immense potential, MPC integration requires careful planning:
- Computational Latency: Encrypted distributed computing is more CPU-intensive and slower than centralized processing.
- Network Communication: Constant data exchange between nodes requires high-bandwidth, low-latency network connections.
- Complexity of Deployment: Implementing MPC requires specialized cryptographic engineering and a robust distributed architecture.
Establishing the Foundation for Secure Digital Infrastructure
- Convergence with AI: MPC will likely power the next generation of “Privacy-Preserving Machine Learning,” where AI models are trained on private, multi-institutional datasets without compromising confidentiality.
- Standardization in Finance: MPC is poised to become the default security layer for Tier-1 banks and global asset managers entering the digital asset space.
- Cross-Border Interoperability: As global regulations tighten, MPC will facilitate secure, compliant data flows between different legal jurisdictions.
Multi-Party Computation is not just an incremental improvement in security; it is a fundamental re-engineering of how we handle digital trust. By resolving the inherent conflict between data utility and data privacy, MPC serves as the cornerstone for the next era of secure digital finance and collaborative enterprise intelligence. For organizations managing high-value assets or sensitive data, MPC is the bridge to a more secure, decentralized future.