In the digital asset ecosystem, security remains the primary objective. As asset valuations and on-chain complexities increase, the risks associated with single-signature control—specifically the vulnerability of a single point of failure—have become a critical liability. Multi-signature (Multi-Sig) technology has emerged as essential infrastructure to mitigate these risks, providing a framework for robust permission management and operational oversight.
Multi-Sig is now the industry standard for institutional-grade protection, utilized for securing exchange liquidity, governing Decentralized Autonomous Organizations (DAOs), and formalizing corporate treasury approval workflows.
The Fundamental Logic of Multi-Sig
Multi-Sig is a cryptographic authorization mechanism that requires multiple independent private keys to validate and execute a transaction.
- Single-Signature: One private key holds 100% control over the associated address.
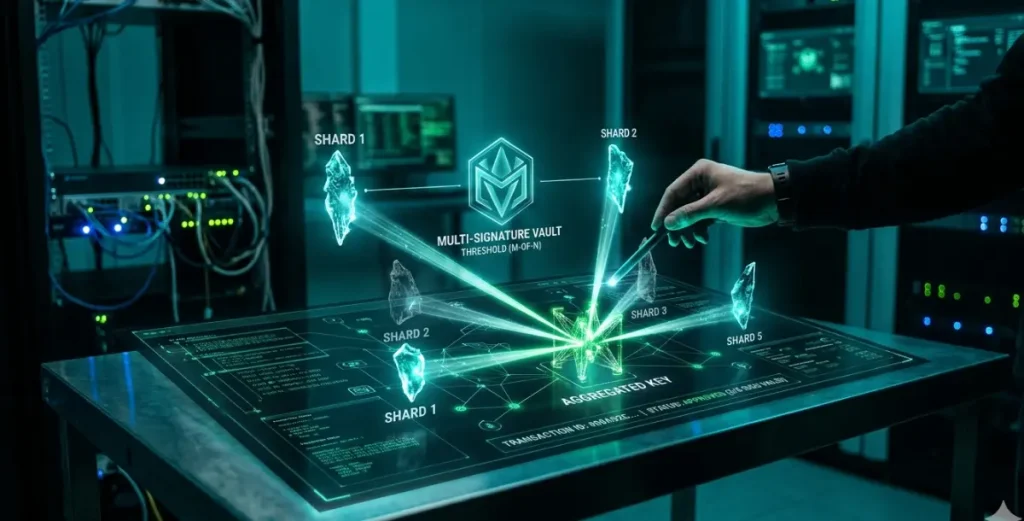
- Multi-Signature: Control is distributed across N keys, requiring a minimum threshold of M signatures to authorize any movement of funds.
For instance, in a 2-of-3 Multi-Sig wallet:
- The wallet is associated with 3 unique private keys.
- Any 2 out of those 3 keys must sign to broadcast a transaction.
- If one key is lost or compromised, the assets remain secure and accessible via the remaining two keys.
Core Operational Workflow
The Multi-Sig process follows a rigorous cryptographic path to ensure decentralized consensus:
- Deployment: A multi-sig address is generated by pre-defining the set of authorized public keys and the required signing threshold.
- Proposal Initiation: Any authorized party can propose a transaction (specifying amount, destination, and data).
- Collaborative Signing: Authorized signers review the proposal and provide their respective cryptographic signatures.
- On-Chain Execution: Once the threshold is met, the transaction is broadcast to the blockchain, verified by the network, and finalized.
Strategic Advantages for Institutional Users
- Elimination of Single Points of Failure: By distributing keys across different physical locations or individuals, the risk of loss, theft, or internal rogue actors is neutralized.
- Exponential Security Scaling: The difficulty of a successful breach increases significantly with each additional signer required.
- Operational Transparency: All authorization steps are recorded on-chain, providing a clear audit trail for compliance and risk management teams.
- Internal Fraud Prevention: No single individual can unilaterally move funds, enforcing a “digital quorum” similar to board-level voting.
Comparative Analysis: Multi-Sig vs. Single-Sig
| Feature | Single-Signature | Multi-Signature |
| Control | Centralized (Single user) | Distributed (Collaborative) |
| Security Profile | High risk of SNoF | Redundant & Secure |
| Operational Speed | Instant | Requires coordination (Slower) |
| Administrative Cost | Low | Higher (Gas & Management) |
| Primary Use Case | Individual/Small-scale | Institutional/Treasury/DAO |
Technical Implementation Methods
1. Native On-Chain Multi-Sig
Supported directly at the protocol level of certain blockchains. It is highly secure and decentralized but often limited in flexibility.
2. Smart Contract-Based Multi-Sig (e.g., Safe)
Implements logic via smart contracts. This allows for highly customizable rules, such as spending limits, whitelisting, and automated role-based permissions.
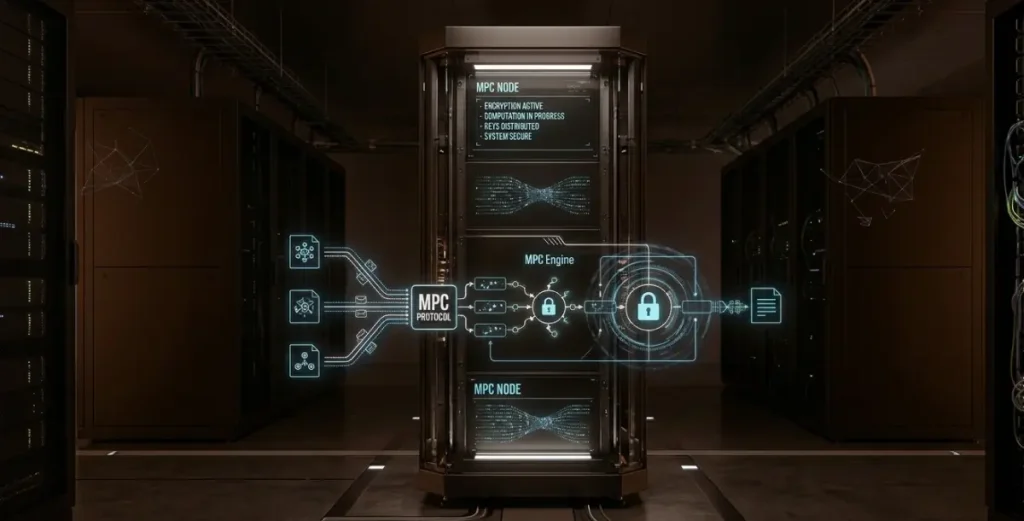
3. Threshold Signature Scheme (TSS)
A cryptographic evolution where a single signature is generated collaboratively without ever reconstructing the full private key. This enhances privacy and reduces on-chain transaction costs.
Key Applications in the Crypto Ecosystem
- Enterprise Treasury Management: Distributing keys among the CFO, CEO, and Risk Officer to ensure every major expenditure undergoes rigorous internal review.
- Institutional Custody: Multi-Sig enables a tripartite management model involving the platform, a third-party auditor, and the client for maximum transparency.
- DAO Governance: Community treasuries use Multi-Sig to ensure that funds are only disbursed after a successful governance vote, with elected “signers” acting as executors.
- Risk Hedging: Preventing individual traders from over-leveraging or moving funds outside of pre-approved strategies.
Challenges and Risk Considerations
Despite its security benefits, Multi-Sig introduces specific operational overhead:
- Coordination Latency: Reaching the required number of signatures can be slow during high-volatility events where rapid execution is needed.
- Signer Collusion: If a majority of signers conspire, they can bypass the minority. Proper selection of independent signers is vital.
- Management Complexity: Maintaining multiple hardware devices and ensuring signers are always reachable requires a robust operational framework.
- Transaction Costs: On-chain Multi-Sig transactions often consume more block space, leading to higher gas fees.
Deployment Best Practices
To maximize the efficacy of a Multi-Sig setup, institutions should:
- Diversify Signer Roles: Assign keys to cross-functional departments (Finance, Legal, Operations) to prevent power concentration.
- Geographic Key Distribution: Store physical backups or hardware wallets in geographically distinct, high-security locations.
- Establish Emergency Protocols: Define clear procedures for “lost key” scenarios or the sudden unavailability of a signer.
- Regular Audits: Periodically review the list of authorized signers and rotate keys if personnel or organizational structures change.
The Future of Multi-Sig
As the digital asset industry matures, we expect to see deeper integration with Institutional Risk Management Systems (RMS) and the widespread adoption of Multi-Party Computation (MPC). These advancements will likely reduce the friction of collaborative signing while maintaining the high-integrity security boundaries that Multi-Sig established.
For any organization managing significant digital capital, a well-configured Multi-Sig framework is no longer optional—it is the bedrock of secure, compliant, and transparent asset governance.