In the digital asset security landscape, Multi-Signature (Multi-Sig) technology represents a fundamental shift in custody logic. By moving away from the “single private key” model, Multi-Sig introduces a decentralized governance structure for asset protection. This framework provides a balance between high-level security and operational flexibility for institutional treasuries, investment firms, and decentralized organizations.
The Mechanics of Multi-Sig Architecture
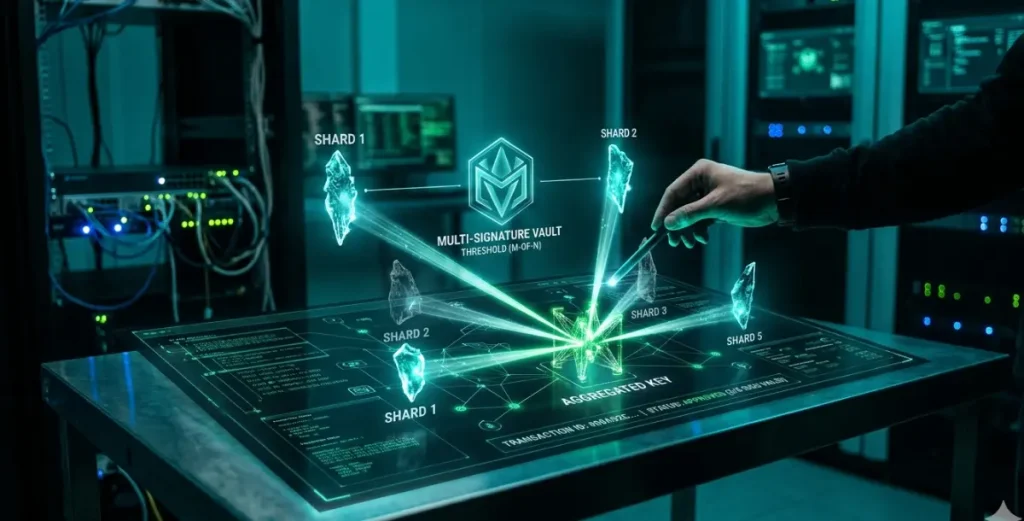
Multi-Sig technology requires a predefined number of independent private keys to authorize a transaction before it is executed on the blockchain. This is defined by a “M-of-N” structure:
- M (Threshold): The minimum number of signatures required to approve a transaction.
- N (Total Signers): The total number of authorized keys associated with the account.
Unlike standard Single-Sig addresses—which create a Single Point of Failure (SPoF) where the loss or compromise of one key results in total asset loss—Multi-Sig distributes risk. An attacker must compromise M independent keys to move funds. Furthermore, the organization can lose up to N-M keys without losing access to the assets, providing a buffer against hardware failure or human error.
Institutional and Professional Use Cases
Corporate Treasury and Governance
Multi-Sig functions as a programmable internal control system. Traditional finance relies on manual approval chains; Multi-Sig encodes these workflows directly onto the blockchain. By distributing keys among executives (e.g., CFO, Treasurer) and independent auditors, companies can mitigate the risk of internal collusion or unauthorized “rogue” transactions. These setups are often enhanced with Time-Locks or Whitelisting to restrict fund movement to pre-approved addresses.
Collaborative Asset Management
In joint ventures or investment partnerships, Multi-Sig ensures co-management. No single partner can unilaterally move assets, effectively mandating consensus for every transaction. Standard configurations such as 3-of-5 or 4-of-7 provide operational continuity even if a key holder is unavailable.
DAO Treasury Management
Decentralized Autonomous Organizations (DAOs) utilize Multi-Sig wallets as their primary vaults. Managed by elected signers, these wallets ensure that treasury outlays occur only after a governance proposal has reached consensus, aligning financial execution with community intent.
High-Net-Worth Security
For individuals managing significant capital, Multi-Sig elevates personal security to institutional levels. A 2-of-3 configuration allows keys to be stored in geographically distinct locations (e.g., a physical safe, a bank vault, and a professional third party). This mitigates risks associated with physical theft, extortion, and accidental loss.
Implementation and Configuration Strategies
Effective Multi-Sig deployment requires a strategic approach to threshold selection and key distribution.
- Threshold Calibration: The M-of-N ratio must be carefully selected. A 2-of-2 setup offers security but no fault tolerance; if one key is lost, the assets are unrecoverable. A 2-of-3 setup is the industry standard for smaller groups, providing a safety net for one lost key. Larger organizations typically favor 3-of-5 or higher to increase the barrier against external breaches.
- Key Diversification: The effectiveness of Multi-Sig depends on the independence of the keys. Signers should utilize diverse storage media (e.g., Hardware Security Modules (HSMs), air-gapped devices, and physical paper backups) and maintain keys across different jurisdictions to prevent localized disasters from compromising the entire set.
- Succession and Recovery Planning: Multi-Sig serves as a robust tool for estate and succession planning. By including a legal entity or executor as a minority signer in a high-threshold configuration, assets can be transferred or recovered in the event of a principal’s incapacitation without granting the third party unilateral control during the principal’s lifetime.
Multi-Sig: Security Advantages vs. Residual Risks
| Category | Key Factors | Description |
| Advantages | Elimination of SPoF | Distributed control ensures that no single private key breach or compromised individual leads to a total loss of assets. |
| Internal Auditing | Transactions require a “digital quorum,” creating a transparent, immutable audit trail of which specific signers authorized a move. | |
| Residual Risks | Operational Friction | High thresholds (e.g., 5-of-9) can cause delays. In volatile markets, the time required to gather signers can impact the ability to access rapid liquidity. |
| Signer Collusion | If the threshold majority (M of N) cooperates maliciously, they can bypass the remaining signers. Mitigation requires diversifying signers across different departments. | |
| Code Vulnerability | For EVM-based Multi-Sigs, security relies on the smart contract. Using audited, industry-standard frameworks like Safe is essential to minimize exploit surface. |
The Evolution of Distributed Control
The industry is currently moving beyond basic Multi-Sig into more advanced cryptographic territories:
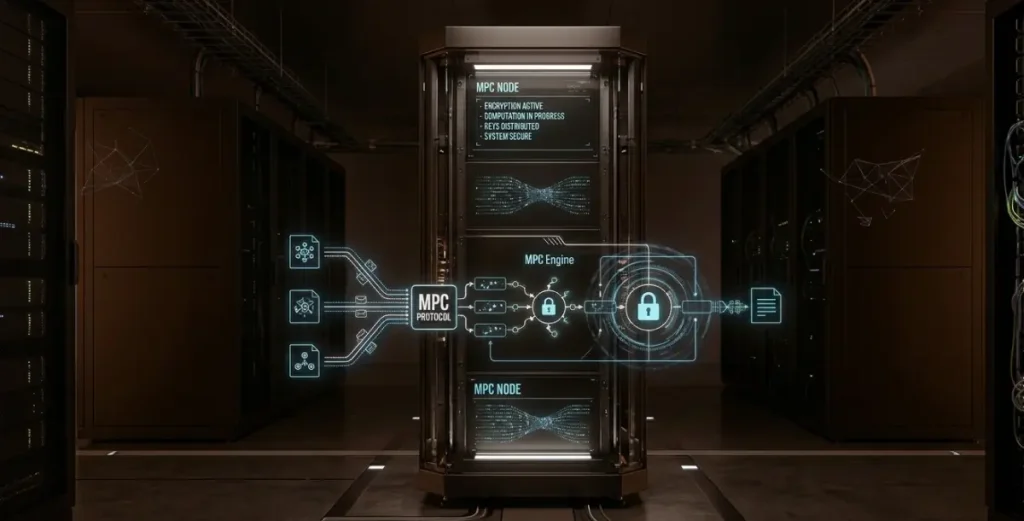
- Multi-Party Computation (MPC): Unlike Multi-Sig, where the blockchain “sees” multiple signatures, MPC allows multiple parties to collaboratively generate a single signature without ever reconstructing the full private key in one location. This offers better privacy and lower transaction fees.
- Programmable Authorizations: Future Multi-Sig iterations will allow for dynamic thresholds—for example, requiring 2-of-3 for transactions under $10,000, but 5-of-7 for anything higher.
- Cross-Chain Interoperability: New frameworks are emerging that allow a single set of signers to manage assets across multiple disparate blockchains through a unified interface.
Multi-Signature technology has evolved from a niche technical feature into the bedrock of institutional digital asset custody. By shifting the security paradigm from “trusting a secret” to “trusting a process,” Multi-Sig provides the structural integrity required for the next wave of institutional capital to enter the digital asset ecosystem with confidence.