As the digital asset market matures, the infrastructure supporting capital protection has evolved beyond basic storage into a critical operational pillar. Digital asset custody now serves as the essential bridge between traditional institutional security standards and the unique cryptographic requirements of the blockchain.
For both individual holders and institutional participants, selecting a custody framework is no longer just a technical choice—it is a foundational risk management decision. This guide analyzes the prevailing custody models, technical architectures, and the criteria for selecting a professional custodian.
The Architecture of Modern Custody
At its core, digital asset custody is the systematic control of private keys. Unlike traditional finance, where assets are held by a central depository, blockchain ownership is defined exclusively by access. Therefore, the custody framework must secure the key throughout its entire lifecycle—from generation to transaction execution.
The industry has moved through three distinct phases:
- The Manual Era: Early adopters relied on primitive methods like paper wallets or basic software interfaces, characterized by high operational risk.
- The Institutional Shift: As capital inflows scaled, the demand for “bank-grade” security led to the rise of professional custodians—entities that combine cryptographic innovation with fiduciary standards.
- The Integrated Future: Today’s landscape is a sophisticated mix of self-custody tools, regulated institutional services, and decentralized management protocols.
Comparative Analysis of Custody Models
| Model | Control Profile | Key Advantage | Primary Risk |
| Self-Custody | Full User Control | Absolute Autonomy | Operational Error / Loss |
| Institutional Custody | Third-Party Managed | Regulatory Compliance | Counterparty Risk |
| Hybrid (MPC/Multi-sig) | Distributed Control | No Single Point of Failure | Technical Complexity |
1. Self-Custody: The Sovereignty Model
This model represents the decentralized ideal where the user retains 100% control of the private keys. While it eliminates counterparty risk, it places the entire burden of security on the individual. It is best suited for participants who prioritize privacy and permissionless access.
2. Institutional Custody: The Fiduciary Model
Users outsource key management to a regulated third party. These custodians utilize hardened infrastructure, including hardware security modules (HSMs) and geographically distributed vaults. This is the standard for corporate treasuries and regulated funds that require external audits and insurance coverage.
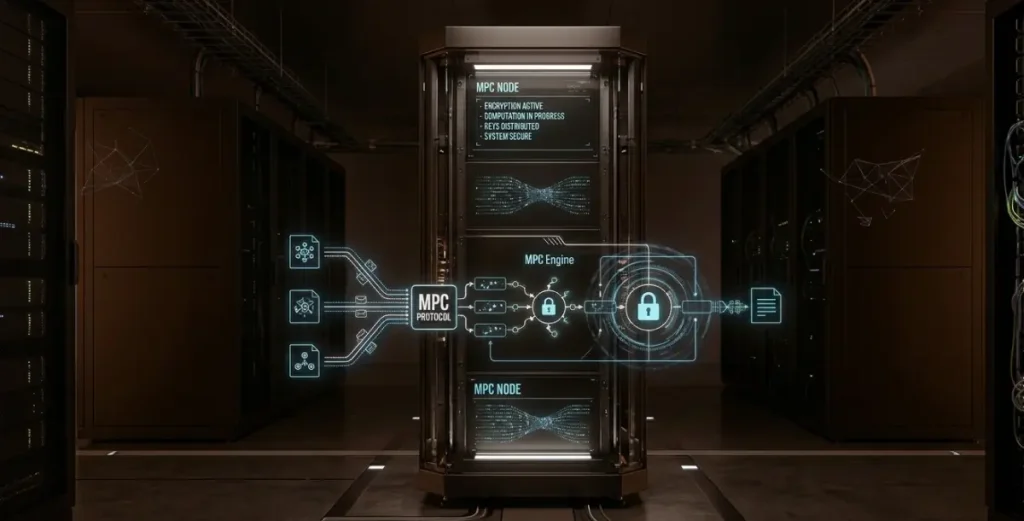
3. Hybrid Custody: The Collaborative Model
By leveraging Multi-Party Computation (MPC) or Multi-signature (Multi-sig) protocols, keys are fragmented across multiple parties. No single entity can authorize a transfer alone, providing a “checks and balances” system that balances security with operational speed.
Technical Security Infrastructure
A professional-grade custody solution is defined by its ability to balance hardened security (keeping keys offline) with operational liquidity (enabling timely transactions).
- Cold Storage (Deep Vaulting): The foundation of asset protection. Keys are kept in permanently air-gapped environments, often within high-security physical data centers. This is where the majority of reserve assets are held.
- Warm/Hot Layers: These layers handle daily transaction needs. While connected to the network, they are protected by rigorous “Whitelisting” of addresses, multi-person approval workflows, and automated velocity limits.
- Key Sharding & Redundancy: Modern solutions no longer store a “whole” key in one place. Using Shamir’s Secret Sharing or MPC, keys are split and distributed, ensuring that even a localized compromise does not lead to a total loss of funds.
Due Diligence when Evaluating a Custodial Partner
When selecting a professional custodian, the evaluation should extend beyond the technical stack to their operational and legal standing:
- Regulatory Licensing: Does the custodian hold the necessary trust or banking licenses in a reputable jurisdiction? This dictates the level of oversight and investor protection.
- Asset Segregation: Ensure that client assets are strictly segregated from the custodian’s balance sheet. In the event of insolvency, segregated assets should remain outside the bankruptcy estate.
- Insurance Coverage: A robust policy should cover both external cyber-attacks and internal collusion. It is critical to understand the specific “loss events” and payout caps defined in the policy.
- Operational Transparency: Look for providers that undergo regular SOC 1 / SOC 2 audits and provide periodic “Proof of Reserves” to verify that assets are actually held on-chain.
The Path to Institutional Maturity
The future of custody lies in operationalizing security. We are seeing a shift where custody is no longer a standalone service but is integrated directly into prime brokerage, staking, and governance.
For the serious market participant, the goal is to move from a “storage” mindset to a “management” mindset. Whether you are managing a personal reserve or a corporate fund, the objective remains the same: eliminating single points of failure while maintaining the flexibility to navigate a 24/7 global market. Establishing a robust custody architecture is the definitive step in moving from passive asset exposure to institutional-grade control.