In the digital asset landscape, your private key is your sovereignty. Regardless of the assets you hold, the security of your private key directly dictates the safety of your portfolio. Among storage methodologies, cold wallets are widely recognized as the gold standard due to their inherent offline nature.
This guide explores the mechanics of cold wallet private keys, secure storage protocols, and risk mitigation strategies to help you establish a robust security framework.
Understanding the Private Key
At its core, a private key is a 256-bit binary number generated via a random number generator, typically represented as a 64-character hexadecimal string or a 12/24-word seed phrase. Within modern cryptographic frameworks, it is computationally impossible to reverse-engineer a private key from a public key.
The fundamental value of a cold wallet lies in its physical isolation from the internet throughout the generation, storage, and signing processes. This “air-gapped” environment eliminates the possibility of remote exploits or malware-based theft. Whether utilizing dedicated hardware or a strictly configured offline computer, the objective remains the same: ensuring the key never touches a network.
Security Essentials in Key Generation
The generation phase is often the most vulnerable point in the security chain. Many asset losses stem from flaws during creation rather than subsequent storage.
- Entropy and Randomness: A secure private key requires a high-quality source of randomness. Any key generated using human-selected patterns or simplistic algorithms is susceptible to brute-force attacks.
- Verified Tooling: Use only open-source tools that have been extensively audited by the security community.
- Physical Environment: Operations should be conducted in a private setting with no network connectivity, cameras disabled, and no third-party observers. If using hardware devices, always verify the integrity of the tamper-evident packaging before use.
Best Practices for Seed Phrase Storage
The seed phrase is the human-readable backup of your private key and is the core of any cold wallet recovery plan. Storing it effectively requires balancing durability with restricted access.
- Metal Backups: To guard against physical disasters like fire, flood, or corrosion, engraving your seed phrase onto stainless steel or titanium plates is the industry standard for long-term preservation.
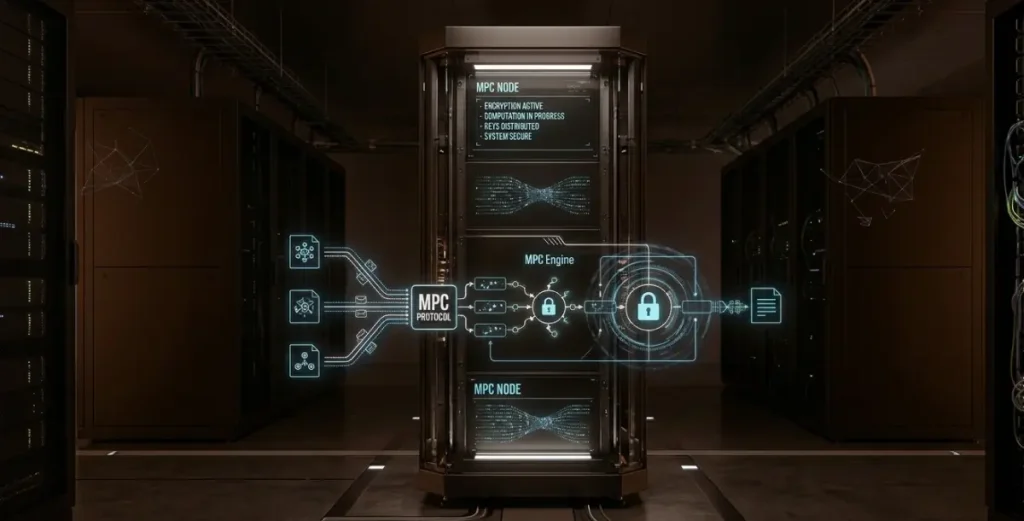
- Geographic Redundancy: Avoid “single point of failure” risks by storing backups in multiple secure locations. Strategies such as Shamir’s Secret Sharing (SSS) can be employed to split the key into multiple parts, requiring a specific threshold (e.g., 2-of-3) to reconstruct the original key.
- The Digital Ban: Never photograph, scan, or upload your seed phrase to any cloud service. Even encrypted digital files on a networked device represent a significant increase in your attack surface.
Secure Transaction Signing: The “Cold-Sign” Protocol
To maintain the integrity of a cold wallet, transaction signing must follow a strict “Cold-Sign, Hot-Broadcast” workflow:
- Construct: Build the unsigned transaction on an internet-connected (hot) device.
- Transfer: Move the unsigned data to the cold wallet via an air-gapped medium (QR codes or a formatted microSD card).
- Sign: Sign the transaction within the offline environment.
- Broadcast: Transfer only the signed data back to the hot device to be broadcasted to the blockchain.
This ensures the private key stays offline, even if the networked device is compromised by malware.
Risk Mitigation and Evolving Threats
No solution is absolute; security is a process of identifying and neutralizing potential vectors.
- Social Engineering: Attackers often pose as technical support or exchange officials. The golden rule is that no legitimate service provider will ever ask for your seed phrase. Any such request is a definitive indicator of fraud.
- Supply Chain Attacks: Procure hardware devices only through official channels or authorized resellers. Perform a factory reset upon receipt and verify the device’s firmware integrity using official tools.
- Multi-Signature (Multi-sig) Frameworks: For high-value holdings, distributing control across multiple private keys—where a threshold of signatures (e.g., 3-of-5) is required to move funds—effectively mitigates the risks of theft or accidental loss of a single key.
Cultivating a Culture of Self-Custody
Cold wallet management is a systematic discipline encompassing secure generation, physical protection, and rigorous signing protocols. Ultimately, the security of your digital assets depends less on the underlying technology and more on the uncompromising nature of your operational procedures.
As attack vectors evolve, achieving sovereign security requires a shift in mindset: security is not a one-time setup, but a continuous process of auditing your protocols and staying ahead of emerging risks. By maintaining an air-gapped environment and treating your seed phrase with absolute physical reverence, you ensure that your assets remain under your control, and yours alone.