As blockchain technology matures and the digital asset market expands, the secure management of these holdings has transitioned from a technical niche to a primary institutional priority. Digital asset custody—the infrastructure designed to secure assets, establish institutional trust, and satisfy rigorous regulatory requirements—is now a foundational pillar of the modern fintech ecosystem.
For digital asset exchanges, payment providers, and fund managers alike, sophisticated custody solutions are an operational necessity. These frameworks ensure asset integrity, maintain regulatory compliance, and mitigate systemic risk. This analysis examines the technical architecture and market trends currently defining the digital asset custody landscape.
Defining Digital Asset Custody
In the digital economy, custody refers to the specialized systems and services provided by third-party institutions to secure the private keys associated with digital assets. Beyond simple storage, it encompasses a comprehensive suite of solutions, including transaction authorization, risk management, and regulatory oversight.
While digital custody mirrors traditional financial custody in principle, it differs fundamentally in its technical execution: in a blockchain environment, control of the private key constitutes control of the asset. Consequently, digital asset custody is, at its core, private key management. The primary objective is to eliminate theft, loss, or unauthorized transfers while maintaining a transparent, auditable record of all activity.
Key Drivers of Institutional Custody
- Mitigating Cyber Risk: Digital assets are high-value targets for sophisticated attackers. Given that blockchain transactions are irreversible, a compromised key often results in permanent asset loss. Institutional-grade custody utilizes multi-layered security protocols to eliminate single points of failure.
- Enterprise Security Standards: Institutional investors manage significant capital and require professional-grade safeguards, including:
- Multi-Party Approval: Implementation of M-of-N signature thresholds to authorize transactions.
- Role-Based Access Control (RBAC): Restricting system access based on specific organizational functions and the principle of least privilege.
- Comprehensive Audit Trails: Real-time logging of all internal and external actions for transparency and forensics.
- Digital and Physical Isolation: Protecting assets through both cryptographic segregation and hardware-level security (e.g., HSMs).
- Regulatory Compliance: Global jurisdictions are increasingly mandating the use of licensed custodians. These requirements often include the strict segregation of client funds, robust Anti-Money Laundering (AML) monitoring, and standardized risk reporting.
- Operational Risk Management: By enforcing rigorous process controls and a clear separation of duties, organizations can prevent internal fraud and mitigate the risk of human error.
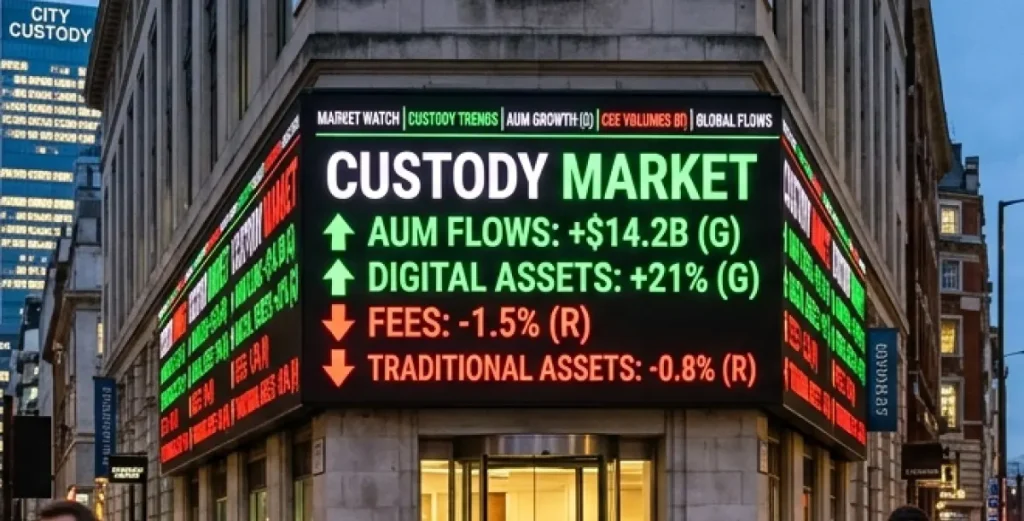
- Market Credibility and Scale: For financial institutions, the quality of their custody infrastructure is a direct indicator of institutional reliability. A robust custody solution is essential for building client confidence and effectively scaling Assets Under Management (AUM).
Comparison of Digital Asset Custody Models
| Model | Core Mechanism | Pros | Cons |
| Self-Custody | Internal management of private keys using proprietary technical tools. | Total autonomy; zero counterparty risk. | 100% security burden; no recourse for lost keys. |
| Third-Party | Assets managed by professional, regulated custodial institutions. | Institutional-grade security; insurance coverage; regulatory compliance. | High counterparty trust required; dependency on provider’s uptime/solvency. |
| Hybrid | Collaborative management (e.g., Multi-Sig or MPC) between the entity and a provider. | Distributed risk; eliminates single points of failure. | Increased operational complexity; requires coordinated workflows. |
Technical Architectures of Modern Custody
Cold Storage
Private keys are kept entirely offline, isolated from internet connectivity. This is the gold standard for securing large-scale, long-term holdings against remote attacks, though it sacrifices transaction speed.
Hot Wallets
Keys are stored in an internet-connected environment to facilitate high-frequency trading and immediate liquidity. While efficient, these are more susceptible to network-based vulnerabilities.
Multi-Signature (Multi-Sig) Technology
Requires multiple independent keys to authorize a single transaction. This prevents a single compromised key from resulting in a breach and is ideal for corporate governance.
Hardware Security Modules (HSM)
Dedicated, tamper-resistant hardware used to generate and store cryptographic keys. These devices ensure that keys cannot be extracted or duplicated.
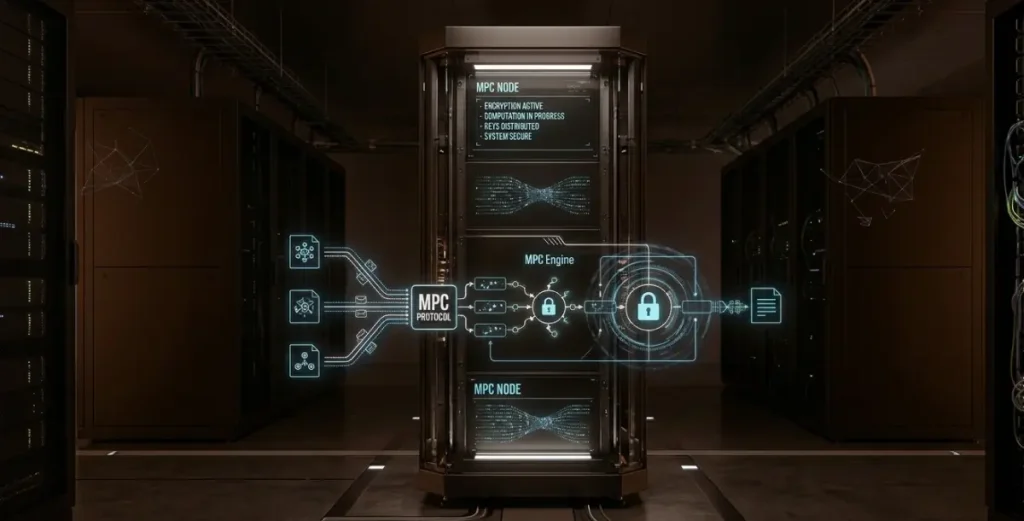
Multi-Party Computation (MPC)
A sophisticated cryptographic method that breaks a private key into multiple “shards” distributed across different parties. No single party ever holds the full key, significantly reducing the risk of internal collusion or external theft.
Engineering a Robust Risk Control Framework
An institutional custody solution is only as strong as its governance. Key components include:
- Role-Based Access Control (RBAC): Defining clear roles for initiators, approvers, and auditors to eliminate single points of failure.
- Real-Time Threat Detection: Continuous scanning for anomalous behavior, such as unusual transaction volumes or suspicious destination addresses.
- Immutable Audit Logs: Maintaining permanent records of every system interaction for compliance and forensic readiness.
- Business Continuity Planning: Utilizing geographically distributed backups and emergency “freeze” protocols to protect assets during unforeseen events.
Digital vs. Traditional Custody: A Comparative View
| Feature | Digital Asset Custody | Traditional Custody |
| Asset Type | On-chain tokens / Cryptography | Securities, Cash, Bonds |
| Control Mechanism | Private Key Access | Legal Title / Book Entry |
| Primary Risks | Cyber hacking, Key loss | Credit risk, Settlement failure |
| Settlement | Near-instant on-chain finality | Centralized clearing (T+1, T+2) |
| Primary Dependency | Cryptography & Code | Legal Frameworks & Institutions |
The Road Ahead: Scaling the Digital Asset Ecosystem
As the bridge between traditional finance and decentralized ecosystems strengthens, we anticipate several key shifts:
- Standardization of Institutional Custody: The industry will gravitate toward unified security and risk management benchmarks.
- AI-Driven Risk Mitigation: Integration of machine learning to identify and preemptively block sophisticated fraud patterns.
- Widespread MPC Adoption: Distributed key management will likely become the standard for balancing security with operational agility.
- Convergence of RegTech: Custody platforms will increasingly integrate native Identity (KYC) and AML tools directly into the transaction layer.
- Interoperable Management: The rise of unified dashboards capable of managing assets across multiple disparate blockchain networks, and Layer 2 solutions.
Future-Proofing Your Custodial Strategy
For organizations evaluating a custody partner or internal build, the decision should hinge on asset scale, operational frequency, and jurisdictional requirements. A robust solution must offer a proven balance between cryptographic security (the “lock”) and operational flexibility (the “key”), ensuring that as the digital economy evolves, their assets remain both accessible and impenetrable.