As the digital asset ecosystem matures, the focus has shifted toward institutional-grade security and individual autonomy. Self-custody has emerged as a critical requirement for blockchain participation, representing the transition from passive holding to direct ownership. Whether for long-term preservation or high-frequency DeFi engagement, the core principle remains: true control is defined by the exclusive possession of one’s private keys.
This guide analyzes the mechanics, strategic advantages, and operational risks associated with self-custody frameworks.
Defining the Self-Custody Framework
A self-custody (or non-custodial) wallet is an architecture where the user retains exclusive control over their private keys and seed phrases. Unlike centralized exchanges or custodial services, the wallet provider has zero access to user funds, no ability to freeze accounts, and no mechanism to recover lost assets.
In this model, the user functions as their own clearinghouse. This eliminates counterparty risk—the danger that a third-party platform might fail, restrict access, or misappropriate funds.
The Mechanics of Direct Ownership
Understanding self-custody requires a clear distinction between where assets are stored and how they are controlled.
- Key-Based Authorization: Digital assets do not “reside” in a wallet; they exist as ledger entries on the blockchain. The wallet is a management interface that uses private keys to prove ownership and authorize the movement of those ledger entries.
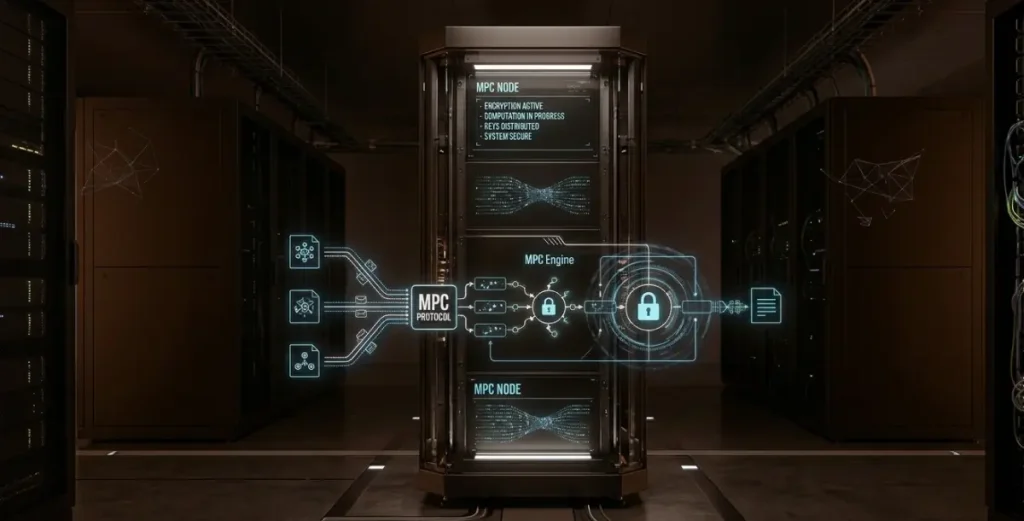
- Localized Signature Generation: Self-custody wallets generate keys locally on the user’s device. During a transaction, the signing process occurs entirely within this local environment. Because the private key is never transmitted to an external server, the user remains the sole signing authority.
Strategic Value of Self-Custody
Self-custody offers several critical advantages for users prioritizing risk mitigation and operational flexibility:
- Elimination of Counterparty Risk: Users are insulated from platform-specific failures, such as exchange insolvency, sudden regulatory freezes, or arbitrary withdrawal limits. This is a primary driver for high-net-worth individuals and corporate treasury management.
- Privacy and Censorship Resistance: Self-custody frameworks bypass the need for centralized intermediaries. Transactions occur directly on-chain, significantly reducing the data footprint left with third parties and ensuring assets cannot be unilaterally frozen by a service provider.
- Unrestricted Ecosystem Access: Self-custody is the native gateway to Web3. It allows for seamless, permissionless interaction with Decentralized Exchanges (DEXs), liquidity pools, and NFT marketplaces without the friction of a middleman.
Operational Risks and Responsibilities
The primary trade-off for total control is the transfer of all security responsibility to the user. This necessitates a disciplined approach to several high-stakes risks:
- Finality of Loss: If a seed phrase is lost, the assets are irrecoverable. There is no “forgot password” feature and no technical support team to reset access.
- Execution Risk: Users are responsible for every parameter of a transaction. A single error—such as sending funds to the wrong address or signing a malicious contract—can lead to an irreversible loss of capital.
- Device Vulnerability: While the service provider cannot access the funds, a compromised local device (via malware or physical theft) can result in key exfiltration if the user does not follow strict hardware protocols.
Comparative Analysis of Custody Models
| Feature | Self-Custody Wallet | Custodial Wallet (Exchanges) |
| Private Key Control | Exclusive User Control | Third-Party Control |
| Recovery Options | None (User-managed) | Fully Supported (KYC/Support) |
| Censorship Risk | Negligible | Moderate to High |
| User Onboarding | Technical learning curve | Low / Intuitive |
| Counterparty Risk | Eliminated | Present |
Best Practices for Secure Management
- Redundant Physical Backups
Seed phrases should be recorded physically—ideally on metal—and stored in geographically dispersed, secure locations. Digital backups (cloud notes, photos, or emails) create a permanent online attack surface and should be strictly avoided.
- Tiered Liquidity Management
Distinguish between “Hot” and “Cold” assets. Use software wallets for small, frequent transactions and Web3 interactions, while keeping the vast majority of holdings in offline hardware wallets.
- Contract and Permission Auditing
Regularly review and revoke smart contract permissions. Malicious or overly broad approvals given to decentralized applications (dApps) can serve as a backdoor for draining assets, even if the private key remains secure.
- Environmental Hardening
Ensure all transactions are conducted on secure, updated systems. For high-value operations, hardware wallets provide a hardened environment that shields private keys even if the host computer is compromised.
The Bottom Line: Transitioning to Direct Control
Self-custody represents the highest level of digital asset maturity. It is the definitive choice for those who value full asset control and privacy over the convenience of a managed service. Choosing self-custody is an intentional decision to trade the safety net of a third-party provider for the absolute security and flexibility of independent management.